The ever-highest increase in Bitcoin price at the start of 2021 has attracted the attention of thousands, resulting in the increasing adoption of cryptocurrencies. At the same time, hacking events are also multiplying. You cannot stop hackers nor regain your assets once your account is hacked or you accidentally lose your private keys. The only thing you can do is to learn how to store crypto securely so that you do not end up empty-handed. Btw, if you want to learn more about investing in crypto, don’t forget to check out our crypto investing course.
Most people do not have the proper knowledge of how they can store crypto. It may be because cryptocurrency is decentralized, and unlike traditional financial systems, people must hold their digital assets on their own.
But No Worries!
Here we have prepared a guide for you to learn different ways to protect and store crypto from hackers and related malicious activities, the safety comparison of wallets, and the best security practices.
Let’s get started!
What is a Crypto Wallet?
Cryptocurrencies are protected by private keys, and a crypto wallet is an app or device that stores these keys. You can use this wallet to access, send or receive your digital assets via keys.
One thing to understand is that a crypto wallet does not store your cryptos. All your holdings are live on the blockchain, which is only accessible via your private keys and can be used to make transactions.
It is imperative to store your keys securely because these are the proofs of your ownership of your cryptos. Therefore, you need to be careful while choosing a crypto wallet.
Types of Crypto Wallets
There are different categories of crypto wallets available in the market. Mostly the choice will have to be made between:
- Hot wallet OR Cold wallet
- Non-custodial OR custodial wallets
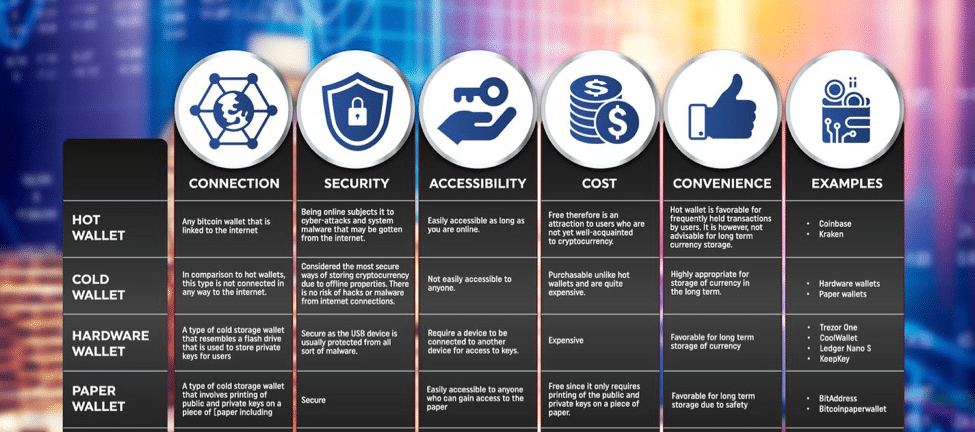
But just before, have a quick look at the summary of types of crypto wallets in the figure below.
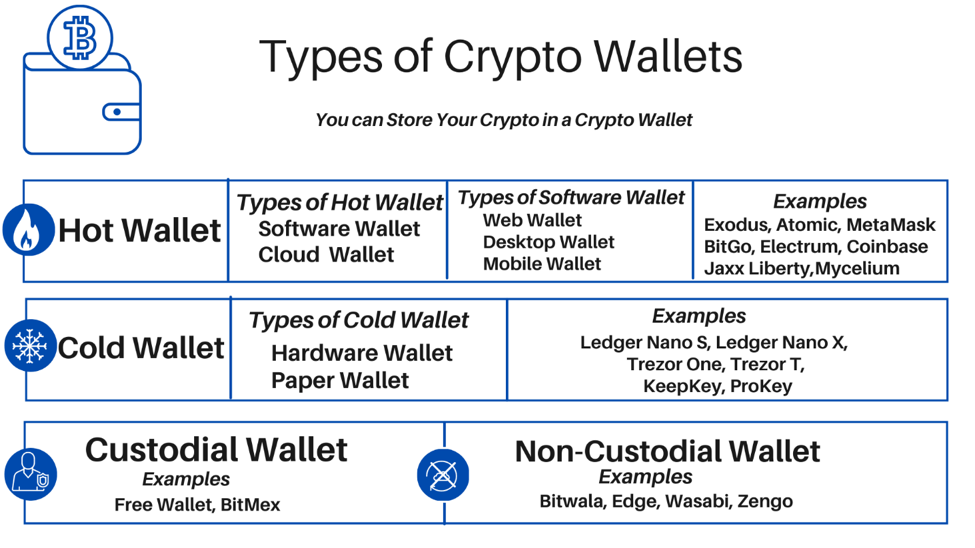
Hot Wallet
A hot wallet is an online cryptocurrency wallet that is connected to the internet. It is the most common type of crypto wallet that can work seamlessly on different blockchains and can be used to make transactions with few clicks.
In a hot wallet, you entrust your private keys to a platform through the internet that is then responsible for managing and securing your keys needed to access and store crypto.
Examples of hot wallets include:
Pros & Cons of Hot Wallets
The following are the benefits of a hot wallet:
- Hot wallets are made for everyday crypto users who make frequent transactions. These wallets are instantly accessible 24/7 in any circumstances.
- These are user-friendly; you can easily install and operate them through their straightforward interface.
- You can use a hot wallet for free, or you have to pay small maintenance fees.
- You do have to worry about securing your private keys because your exchange platform will be doing it for you.
The following are the cons of a hot wallet:
- Hot wallets may be prone to vulnerable attacks because your keys are stored on the internet.
- Hot wallets involve dependency on the exchange so, you don’t have full control of your assets, and even for transactions, you need an intermediary.
- If the exchange you trust with your keys turns out to be fake, you will lose everything.
Cold Wallet
A cold wallet is a physical cryptocurrency storage that is not connected to the internet. You will only require connecting your wallet to the internet to make transactions.
In the case of cold storage, you hold your cryptographic keys offline without depending on third parties.
The transactions through cold crypto wallet take place offline, which requires a signing process through keys. In actuality, the transaction is initiated online but then moved offline to digitally sign it, which removes the risk of leaving private keys online.
Examples of cold wallets include:
- Ledger Nano X & S
- Trezor One & T
- KeepKey
- ProKey
Pros & Cons of Cold Wallets
The following are the benefits of a cold wallet to store crypto:
- A cold wallet is more secure than a hot wallet because you do not entrust any third-party exchange with your cryptographic private keys.
- It cannot be hacked because it is not connected to the internet.
- A cold wallet is a better option when storing a large number of digital assets.
The following are the cons of a cold wallet:
- Unlike a hot wallet, a cold wallet will cost you $100 on average to buy.
- Cold wallets do not support many cryptocurrencies.
- The transactions through cold wallet may take time which may not be convenient for day traders.
Now let’s have a quick look at the differences between hot wallets and cold wallets mentioned in the picture given below.

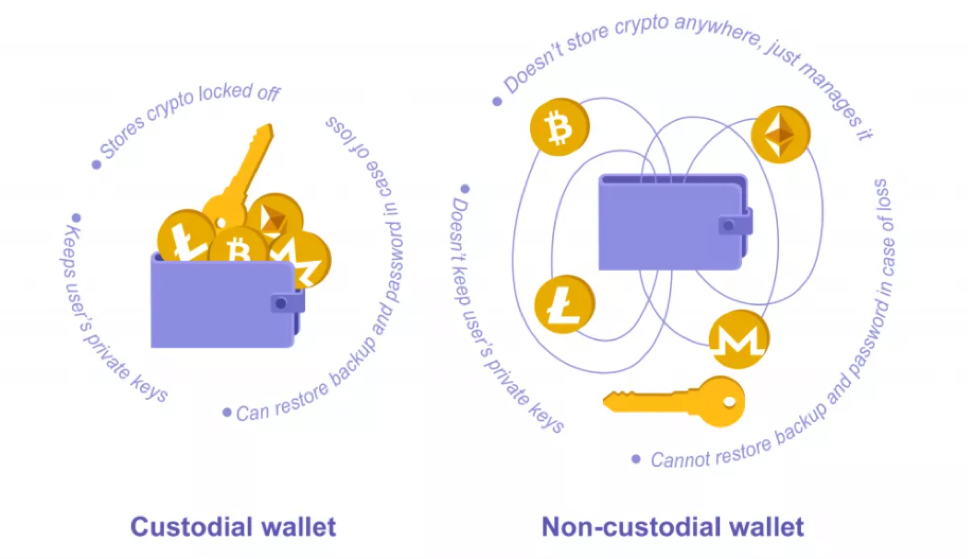
Non-Custodial Wallet
A non-custodial wallet is an online wallet in which the user is the sole owner of the private keys. The user has full control over his funds, and no one can make transactions on his behalf.
Examples of non-custodial wallets include:
- Bitwala
- Sawabi
- Edge
- Zengo
Pros & Cons of Non-Custodial Wallet
The following are pros of a non-custodial wallet:
- In non-custodial wallets only, the user is responsible for his keys; therefore, only you can authorize any transaction.
- Users can make instant transactions without depending upon intermediaries.
- There is less risk of data breaches.
The following are cons of a non-custodial wallet:
- There can be a risk of attacks as the wallet is connected to the internet.
- If you make any mistake, there will be no way of undoing it. Even a typing mistake can result in loss.
Custodial Wallet
In a custodial wallet, you hand over keys to a third party that controls your private keys. The user depends on an exchange platform for making any transaction. If something happens to that exchange, such as a hacking attack, you can lose access to your wallet and ultimately to your digital assets.
Examples of custodial wallets include:
- FreeWallet
- BitMex
Pros & Cons of Custodial Wallet
The following are pros of a custodial wallet:
- A trusted exchange can help you not losing access to your assets.
- Users can make a transaction without paying any fee within the ecosystem.
- You can retrieve your funds if you make any specific mistake that your chosen platform can solve.
The following are cons of a custodial wallet:
- You do not have full control over your funds and keys.
- Your account can be locked if the platform finds you involved in suspicious activity.
- There are chances of data breaches.
- You will lose your assets if the exchange is hacked.
The picture given below shows the difference between custodial wallet and non-custodial wallets.
Up till now, you have learned about the main types of crypto wallets to store crypto, now you will study their subcategories. Keep reading!
Types of Hot Wallets
Hot wallets are further categorized as software wallets, and cloud wallets. Let’s understand them.
Software Wallets

Software wallets fall under hot wallets because they are connected to the internet, often with an exchange.
Software wallet comes in various forms such as web wallets, desktop wallet, and mobile wallets which are discussed below.
Web Wallets
As the name suggests, a web wallet is accessible through a web browser without downloading any specific app or software on your device. When using web wallets, the website holds private keys and crypto, which gives you less control as you become dependent on the website.
There is also an option of a multi-sig wallet that offers two keys. The website offering a multi-sig wallet will keep one key, and the other will be yours. It gives more control to users over their assets, comparatively.
Web wallets are also called online wallets and are very easy to use as you can access your digital assets from anywhere on any device with your password.
Desktop Wallets
Desktop wallets are computer programs that hold your private keys on your PC. You will need to download the app, which will be password protected and can only be accessible by the user.
On downloading the application, you will generate your password to access the wallet and a data file to hold your keys.
Before downloading the desktop wallet, you must ensure your computer is free from viruses or malware.
Do not forget to back up your data so that you do not have to face difficulty if something happens to your PC.
Mobile Wallets
Mobile wallets are made for use on smartphones. These are easily accessible anytime and anywhere. You can make quick payments via QR codes using these wallets.
Using mobile wallets, you will be storing your keys on your mobile device. If your mobile goes missing, you will lose your private keys.
However, these wallets can be vulnerable to various malware & virus, so you need to be careful.
Most Popular Software Wallets
The following are some of the most popular software wallets available.
Exodus Wallet

Exodus is one of the most popular software wallets that supports more than 110 cryptocurrencies, including Bitcoin (BTC). It is a desktop and mobile wallet that allows users to control their private keys.
Exodus is a partnership with several exchanges to offer support and swap services on a broader range of cryptocurrencies. It is free of cost service and is almost supported by all major platforms providing excellent customer service.
However, the wallet charges a small fee for facilitating transactions within the ecosystem. Also, transaction fees are paid to only miners depending upon the size of the transaction.
It is the best wallet for beginners with straightforward interphase, support system, and essential features. Exodus team ensures the security of the wallet.
Atomic Wallet
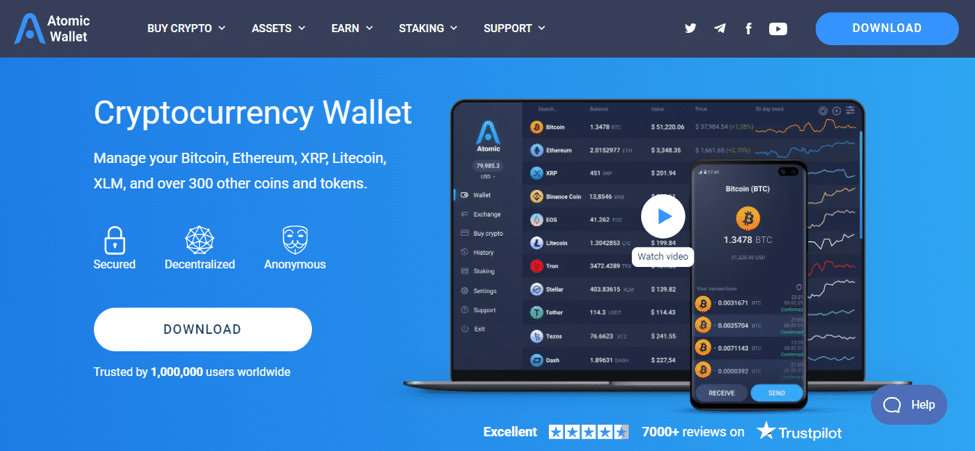
Atomic wallet is a desktop wallet that users to have full control over their assets and private keys as all information is stored on users’ computers.
It supports more than 300 cryptocurrencies, including ERC-20. You can download this app for free, but it does charge some service fees on transactions through ShapeShift, crypto purchases with a credit card, and P2P currency transactions within the wallet.
Users do not have to fill in their personal information nor depends on intermediaries for executing transactions.
Users receive a unique “ backup phrase” to recover access to their wallets in case of any mishap.
BitGo Wallet
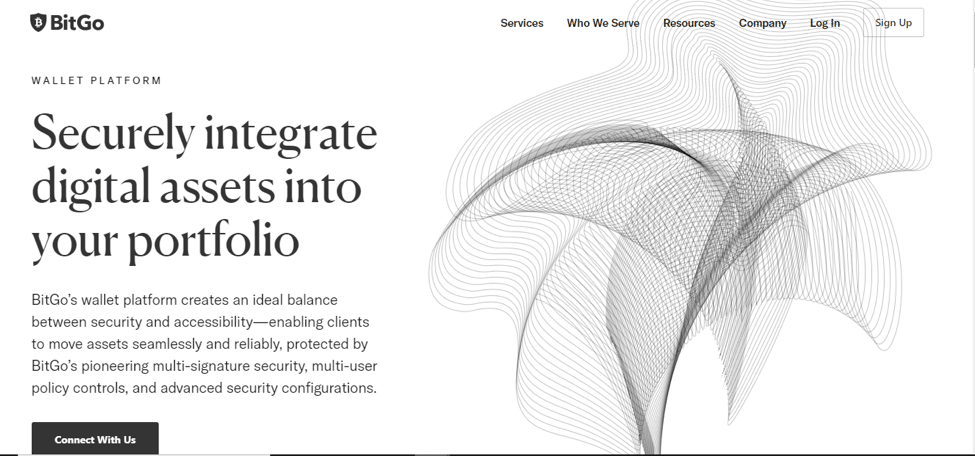
BitGo is a web wallet that can easily be connected through a PC, laptop, etc. It supports nearly 90 cryptocurrencies.
BitGo wallet has three keys; one is for the user, the second is stored on the platform, and the third is stored through the Key Recovery Service software of BitGo (this service generates and secures private backup keys).
Each transaction requires two signatures for completion without involving third parties.
BitGo ensures security through two-factor authentication and IP confirmation whenever the user login his wallet.
Other Software Wallets to Try
You can also check the following software wallets.
- Electrum Bitcoin Wallet: It is a reliable wallet by which the user stores his private keys in his computer in an encrypted form that is not seen by the server. It can be easily synchronized on different devices to import or export keys. It is a free service that offers advanced features and only supports Bitcoin (BTC).
- Jaxx Liberty: It is a software wallet available for Windows, Linus, Android, IOS, etc. It supports more than 80 cryptocurrencies and is a free service. The wallet has integrated ShapeShift for quick transactions. Users control private keys.
Do check out Bitcoin Core and Mycelium hot wallets as well.
Cloud Wallet
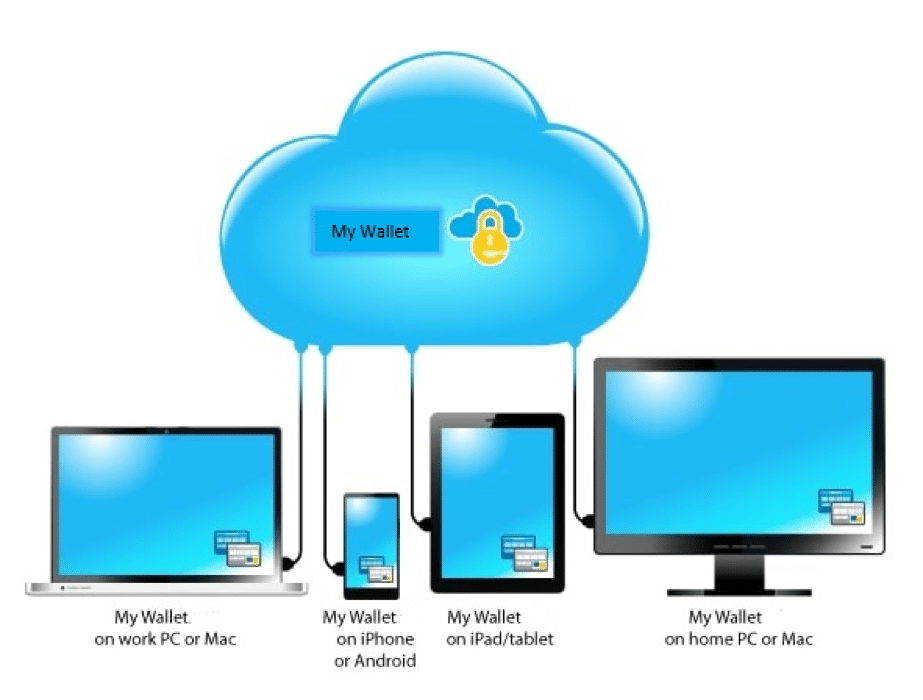
Cloud wallet falls under the category of hot wallets.
You can access your crypto assets from any computer, device, or geographical location using a cloud wallet. They are very convenient to use but can store your private keys online. Third parties can control these wallets; therefore, there are more chances of vulnerability.
A cloud wallet allows you to store an encrypted copy of your recovery phrase on your personal cloud that will be password protected. If you lose your device or accidentally signed out of the app, you can easily regain access to your cryptos via your cloud account and password.
Examples of cloud wallets include:
- Coinbase
- Binance
- MetaMask
- Blockchain.info
Coinbase Wallet
Coinbase wallet allows users to store and buy & sell cryptocurrencies. It supports different cryptocurrencies, including Bitcoin (BTC), Litecoin (LTC), Ethereum (ETH), etc. It has simple interphase, which is very convenient for novices.
Coinbase wallet being in the cloud does not require downloading a chain of blocks that could eat up a lot of space on your computer. Using Coinbase cloud wallet, users are provided with privacy that not even the platform can access or know the password.
Coinbase wallet offers security by putting a limit on daily withdrawal and enabling 2-factor authentication. It also keeps 98% of the funds on the platform in the cold storage resultantly; if there happens any hacking attack, the platform users will not lose more than 2% of their funds.
This was all about hot wallets. Now let’s learn about categories of cold wallets.
Types of Cold Wallets
Hardware wallets and paper wallets are subcategories of cold wallets. Let’s understand them.
Hardware Wallet

Hardware wallets are the most secure way to store crypto. A hardware wallet saves your private keys on a physical device- similar to a USB drive, and it is not connected to the internet.
For making transactions, the device will ask for transaction details and validates the data itself. In this way, your private keys always remain on your device.
A hardware wallet can efficiently work on different blockchains and support different cryptocurrencies, so it is the best option for those investors with a large number of cryptos.
It can be more expensive than a software wallet as it provides enhanced security comparatively.
Examples of hardware wallets include:
- Ledger Nano S
- Trezor One
- ProKey
Most Popular Hardware Wallets
The following are the most popular hardware wallets, to store crypto, that available in the crypto market:
Ledger Nano S Hardware Wallet
Ledger Nano S is the widely used hardware wallet for crypto storage introduced by Ledger (France). This wallet is compatible with different blockchains and supports around 1184 coins, including Bitcoin (BTC), Bitcoin cash (BCH), Binance Coin (BNB), Cardano (ADA), Ethereum (ETH), Litecoin (LTC), etc.
Using Nano S, the user can undergo the entire recovery process from the wallet without even connecting it to the PC or laptop.
It is the best option to secure crypto for a fair price. It is effortless to use, proving to be an excellent choice for beginners.
Ledger S does not come with a USB Type-C cable which may be inconvenient for smartphone users.
Ledger Nano X is another Ledger hardware wallet that almost works similar to Nano S with some increased features.
Trezor Hardware Wallet
Trezor is one of the first Bitcoin hardware wallets created by Satoshi Labs. It can be used with Android devices.
Trezor ensures security by offline transaction signing, and each wallet has a PIN code that never leaves the wallet. It protects the user’s private key even if the computer is infected by malware. You can recover your Trezor wallet even if you lose it.
Trezor One and Trezor T are Trezor wallets out there.

Trezor One requires you to enter the PIN randomly generated by your wallet and displayed on its screen. After entering the PIN, you will need to enter a passphrase, only which you know. After this, you can access your cryptos. Trezor One wallet supports 1064 coins. It can be used on all devices such as Windows, Linus, Mac, etc.
It does not support Cardano (ADA), Ripple (XRP), Monero (XMR), and Tezos (XTZ).
Trezor T is an improved version of the Trezor One hardware wallet. It is entirely touchscreen. It supports a large number of coins, including those coins that Trezor One does not support. It can also be used on all devices, i-e Windows, Linus, etc. It randomly generates PIN code to keep device and transactions secure and never exposure your private keys.
It is a little expensive than Trezor One wallet.
Other Hardware Wallets to Try
You can also try other alternative wallets to store crypto:
- KeepKey Hardware Wallet: It offers security via PIN confirmation and recovery chipper. It is designed to be user-friendly with its large LCD and ability to withstand wear and tear. It has integrated ShapeShift to improve transaction speed. It does not come with a lock feature; therefore, you must always be careful when using it.
- ProKey Hardware Wallet: It is an excellent option for crypto beginners and veterans with its unique features. It supports more than 1500 coins and tokens. It is transparent and easy to use that protects against hacks via secure firmware. It was founded in 2018.
You have made a great progress! Now you will read about the second category of cold wallets i-e Paper wallet.
Paper Wallet
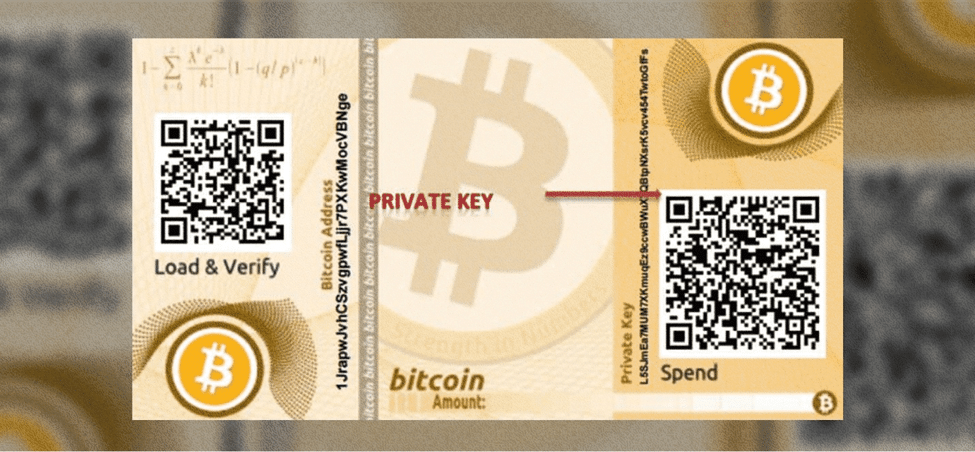
A paper wallet is a piece of paper that contains all the details required to access your cryptos. The non-digital nature of this wallet can be a great alternative to store crypto. The details include keys and QR codes printed on paper.
A paper wallet is not connected to the internet, so it is considered more secure, but there are also risks associated with it, such as losing or damaging the paper. If you lose the paper, you will lose access to your funds as well.
Top Companies Generating Paper Wallets
- Walletgenerator.net generates paper wallets that eliminate the risk of sending private keys on the internet. This service is free to use.
- Bitcoinpaperwallet.com generates a paper wallet that is super easy to use. It creates paper wallets that are colorful and with perfect fold lines.
Mycelium, Verge paper wallet generator, Bitaddress.org, etc., are also among the top paper wallet generators.
Comparison of different types of crypto storage wallets
Best security practices to protect your private keys
Once you have selected your crypto wallet, the following are few best practices that you must take to ensure security at your end when you need to store crypto.
- Update your software wallet frequently as soon as updates are available; avoid using old versions.
- Always use two-factor authentication to access your account.
- Use antivirus software to detect and wipe out viruses and malware, whether your wallet is connected to the internet or not.
- Always backup your wallet as often as you can to always have a way to recover your assets if anything happens to the device.
- Always use a unique and strong password to protect your wallet.
- Store your password securely either at a safe place or memorize it. Because if you forget your password, you will no longer have access to your assets.
Recently a story went viral in which a Bitcoin owner forgot his wallet password and lost access to $220 million worth of his Bitcoin assets.
- Use a separate email to ensure extra security.
- You can also implement multiple signatures that will require approval from various people to complete a transaction.
- Keep your private keys to yourself; never share with anyone or on social media.
- Avoid scam phishing emails that promise giveaways. Never click on untrusted links, emails, or attachments.
- Use a secure WiFi connection. Avoid using public WiFi.
The bottom line
Storing cryptocurrency and private keys is not difficult; only you need to be more active and conscious regarding security. Choose a wallet carefully after analyzing your requirements in terms of crypto storage.
When you are in the crypto industry, it is a must for you to do homework before taking any step.
Cryptocurrency is here to stay with a bright future ahead, so do not hesitate to educate yourself to gain more confidence in your crypto dealings.
Choose Wallet Wisely, Use Crypto Boldly! We hope that you have learned a lot from our guide to how to store crypto. You can also check out our other articles to read more knowledgeable content.








